Attack Frameworks & Exploitation
Professional-grade offensive security tools integrated into a single native interface. No terminal juggling, no config files — just point and attack.
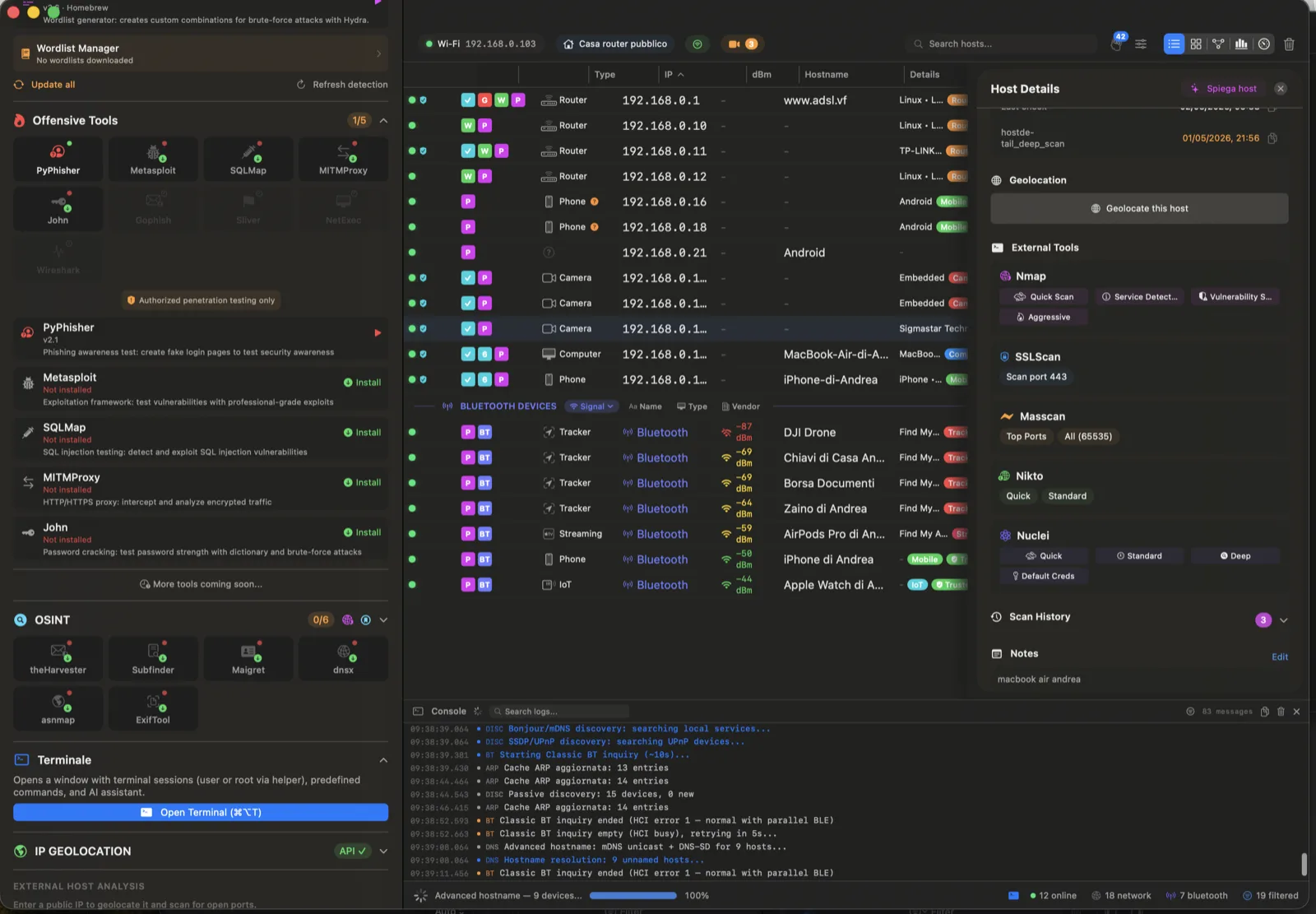
🎣 PyPhisher
Launch phishing campaigns with 30+ templates. Hosts fake login pages, captures credentials in real time, tracks campaign statistics. Includes Cloudflare tunnel for external access.
OFFENSIVE🐙 Bettercap
Full MITM framework: ARP spoofing, live packet sniffing, HTTP/FTP/SMTP credential capture, JavaScript injection into web traffic, caplet automation, REST API control.
OFFENSIVE💣 SQLMap
Automated SQL injection detection and exploitation. Tests GET/POST parameters, supports tamper scripts, extracts databases, tables, and credentials from vulnerable targets.
OFFENSIVE🔀 MITMProxy
Transparent HTTPS interception proxy. Inspect, modify, and replay HTTP/S traffic in real time. Certificate generation for SSL/TLS interception.
OFFENSIVE